A cloud-based model is standard for storing and accessing data, and it’s more important than ever to ensure that this data is secure. Unfortunately, the rise of cloud technology has also coincided with a sharp increase in the number and sophistication of cyber attacks. In this blog post, we’ll look at some of the top threats to cloud security and the steps to protect them.
Cloud system breach
There are several different ways that criminals can exploit vulnerabilities in cloud-based systems. Some of the most common include:
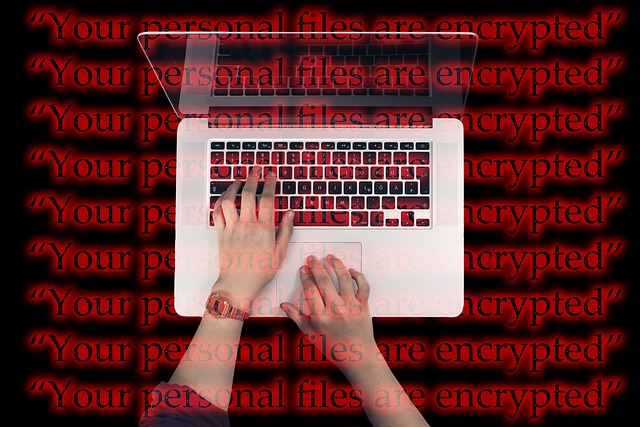
Data Breaches: An unauthorized user has access to sensitive data. It can be done through hacking, social engineering, or other methods. Once inside a system, hackers can access customer records, financial information, intellectual property, or different data types. Data breaches harm businesses and customers, including economic loss, reputation damage, and trust loss.
Denial of Service Attacks: A denial of Service (DoS) attack is when an attacker prevents legitimate users from accessing a system or service. It floods the targeted party with requests that overload the system and prevent it from responding to legitimate traffic. DoS attacks can disrupt businesses and cause financial losses. They can also be used as a distraction while another type of attack is carried out.
Imitation/Spoofing Attacks: A fraud or spoofing attack is when an attacker creates a copy of a website or service to trick users into providing sensitive information such as login credentials or credit card numbers. This attack is often used to commit fraud, theft, gather intelligence, or launch further attacks.
Phishing Attacks: Phishing is a type of social engineering attack in which an attacker uses deception to trick victims into getting sensitive information or infecting their systems with malware. Phishing attacks are often sent via email or text message and may contain links to malicious websites or attachments that have malware.
How to secure Cloud Technology?
As businesses increasingly move to cloud-based systems, they must ensure they are secure.
Data encryption:
One way to do this is to encrypt data at rest and in transit. Data at rest includes information stored on servers, while data in transit refers to information sent between servers. Encryption helps to protect data from being accessed by unauthorized individuals.
Role-based access:
Another way to secure cloud technology is to use role-based access controls. It is a type of control that limits what users can see and do based on their assigned roles and is called Identity and Access Management.
For example, an administrator might have access to all system areas. In contrast, a customer service representative might only have access to the part of the system that deals with customer accounts. By carefully controlling user access, businesses can help to prevent unauthorized individuals from gaining access to sensitive data.
Strict monitoring and reviewing:
Finally, reviewing security procedures and updating them regularly as needed is essential. By staying up-to-date on security best practices, businesses can help to ensure that their cloud-based systems are secure.
As the world increasingly relies on cloud-based systems, it’s essential to be aware of the growing threat landscape. Understanding the most common types of attacks and taking steps to protect your data can help keep your business safe from harm.